DataTako for cybersecurity
Deliver live threat intelligence, SOC reporting, and compliance dashboards through a branded, enterprise-grade portal — no Power BI licenses required for your clients.
Distributing threat intelligence, SOC metrics, and compliance evidence to clients requires security-first delivery, not email attachments.
Emailing SOC reports, incident briefs, and threat write-ups exposes your clients' security posture the moment it lands in an inbox.
Generating and sending per-client threat briefings or compliance packs doesn't scale as your MSSP book of business grows.
Buying a Power BI Pro license for every analyst, CISO, and auditor who needs visibility inflates your operating cost.
Ensuring each client only sees their own detections, incidents, and posture metrics is a continuous access-control burden at scale.
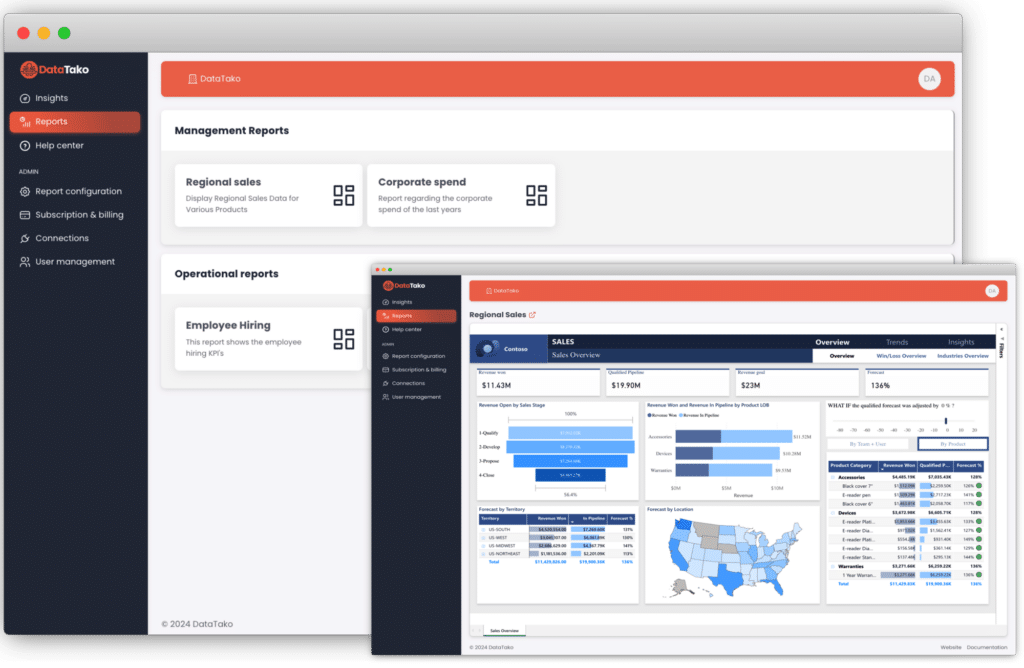
Everything a cybersecurity firm needs to share threat intelligence and compliance reports with clients — safely and at scale.
Brand the portal with your firm's logo, colors, and domain. Clients experience your cybersecurity brand, not a third-party tool.
Share interactive Power BI reports with unlimited external users without buying Pro licenses.
Each client only sees their own data. Secure, isolated, and fully compliant.
Add and remove client users in seconds. Group them by organization for easy oversight.
Reports update automatically. Your clients always see the latest data without manual intervention.
Sub-organisations let you manage dozens of MSSP clients from a single workspace with fully isolated reporting environments.
From MSSP threat reporting to SOC 2 and ISO 27001 audit delivery, DataTako streamlines how security firms share sensitive insights.
01
Give each managed client a branded portal showing their detections, incident timeline, and SIEM dashboards — updated in real time.
02
Share SOC 2, ISO 27001, and PCI DSS evidence packs that auditors can filter, explore, and export straight into their workpapers.
03
Run a single analytics workspace while each client, region, or business unit sees only their own security telemetry — enforced at the dataset level.
✗
Emailing incident reports and threat briefs as attachments
✗
Paying for a Power BI Pro license per client analyst
✗
Manual tenant separation for every new report
✗
Static PDFs outdated before clients even open them
✗
Generic Power BI URL that doesn't reflect your brand
✓
Secure portal access with full audit trail
✓
Zero client-side licenses required
✓
Automated data isolation via row-level security
✓
Real-time dashboards always current
✓
Fully branded with your firm's identity
Your clients data is protected at every level.
Each client only sees their own data, enforced at the Power BI dataset level.
Built on Microsoft Azure with enterprise-grade uptime and reliability.
Granular permissions let you control exactly who sees what, down to the report level.
SSO support and secure login flows keep your client accounts protected.
See how DataTako helps cybersecurity firms share threat intelligence and compliance reports through a secure, branded portal.
Common questions from Cyber security agencies exploring DataTako.
DataTako combines user-level access controls with Power BI row-level security. You can define exactly which users see which reports, and within each report, which data rows are visible to each user.
Yes. DataTako's portal is fully responsive. Your clients can review financial dashboards from any device — desktop, tablet, or smartphone — with the same interactive experience.
Absolutely. With sub-organizations and row-level security, you can serve multiple entities from a single Power BI workspace. Each entity sees only their own financials while you manage everything centrally.
Yes. You can build comprehensive financial dashboards in Power BI and share them securely through DataTako. Clients can filter by period, account, or entity and export views for audit documentation.
DataTako enforces row-level security at the Power BI dataset level, ensuring each client only sees their own financial data. The platform runs on Microsoft Azure with enterprise-grade encryption and access controls.